Nautobot Firewall Models¶
Overview¶
A plugin for Nautobot that is meant to model layer 4 firewall policies and/or extended access control lists.
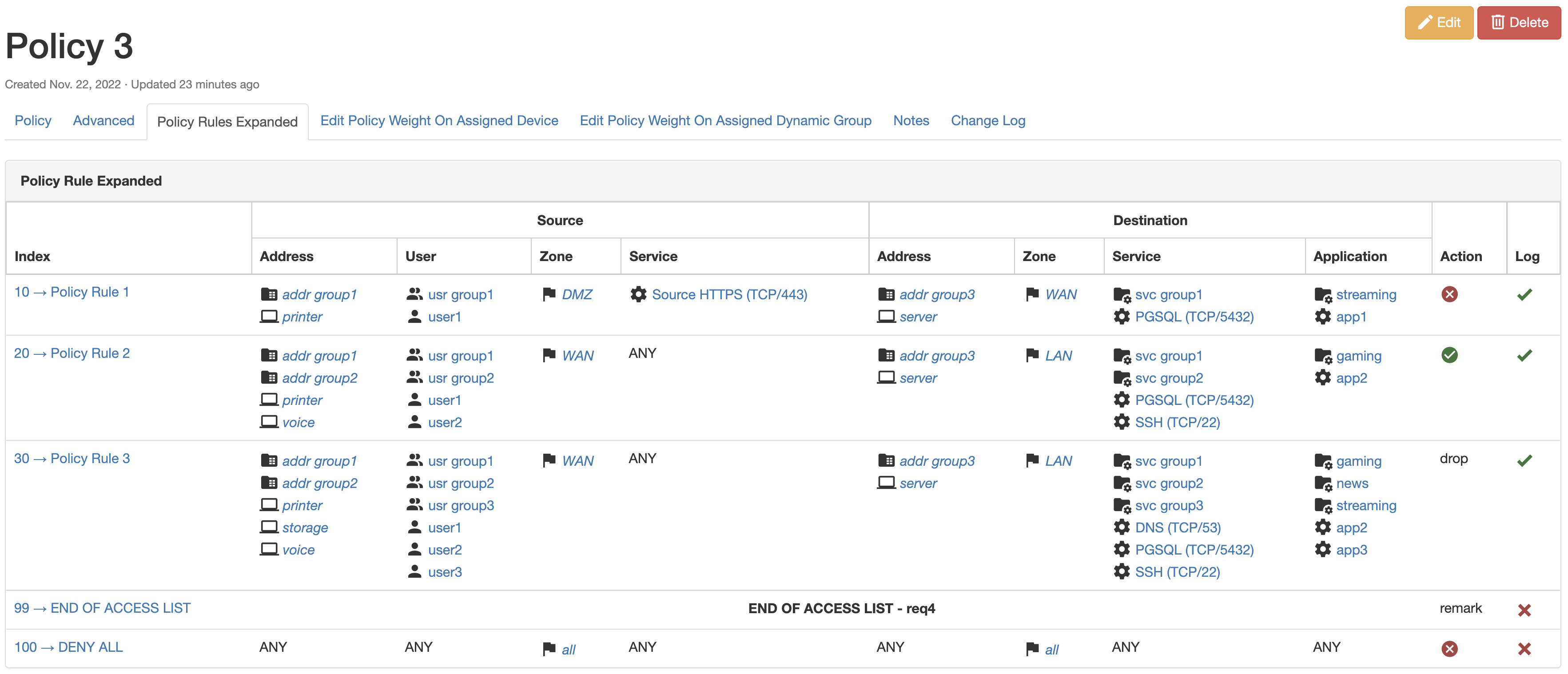
Screenshots¶
More screenshots can be found in the Using the App page in the documentation. Here's a quick overview of some of the app's added functionality:
Try it out!¶
This App is installed in the Nautobot Community Sandbox found over at demo.nautobot.com!
For a full list of all the available always-on sandbox environments, head over to the main page on networktocode.com.
Documentation¶
Full documentation for this App can be found over on the Nautobot Docs website:
- User Guide - Overview, Using the App, Getting Started.
- Administrator Guide - How to Install, Configure, Upgrade, or Uninstall the App.
- Developer Guide - Extending the App, Code Reference, Contribution Guide.
- Release Notes / Changelog.
- Frequently Asked Questions.
Contributing to the Documentation¶
You can find all the Markdown source for the App documentation under the docs folder in this repository. For simple edits, a Markdown capable editor is sufficient: clone the repository and edit away.
If you need to view the fully-generated documentation site, you can build it with MkDocs. A container hosting the documentation can be started using the invoke commands (details in the Development Environment Guide) on http://localhost:8001. Using this container, as your changes to the documentation are saved, they will be automatically rebuilt and any pages currently being viewed will be reloaded in your browser.
Any PRs with fixes or improvements are very welcome!
Questions¶
For any questions or comments, please check the FAQ first. Feel free to also swing by the Network to Code Slack (channel #nautobot), sign up here if you don't have an account.

